Recent news about how effective Anthropic’s Mythos model is at identifying new vulnerabilities has prompted much debate and hand wringing. According to the reports (I’m not one of the VIP’s with a personal invitation to study this model) it can’t just quickly identify previously unknown weaknesses in software and services. It can also to string together multiple exploit tactics to develop an attack plan.
This is an unsettling outlook; what is its broader effect going to be on business’ cyber security postures?
The Pre-Mythos Situation
Organisations struggle to manage and address vulnerabilities quickly. It is a relentless task, fraught with the anxiety that a patch will break a business critical system or process. Too frequently though, avoiding the risk of a bad patch is seen as attractive without adequately considering the impact of a security breach caused by a proliferation of system weaknesses.
While the problem of vulnerability management may be hard, that doesn’t mean it is conveniently unnecessary. Threat actors exploit vulnerabilities – it is as simple as that. Leaving one exposed in the wrong place is like leaving your front door wide open (or at least unlocked) when you go away on holiday. This is why the UK’s National Cyber Security Centre has tightened up its assessment approach for the Cyber Essentials Plus standard (Important Update: Changes to Cyber Essentials for April 2026 – IASME – Home).
How has the Mythos revelation changed the dynamics
The situation before Mythos like capabilities was already challenging. New vulnerabilities were identified on a daily basis, and (responsible) vendors would rush out fixes in the hope that their customers would stay one step ahead of the threats.
And then Anthropic discovered that Mythos was surprisingly capable at identifying vulnerabilities, including a multitude of weaknesses that were not known before.
These so-called Zero Day vulnerabilities (so called because the vendor’s have no time to prepare a fix before they are exploited) used to be the preserve of nation state agencies who would save them for their most important operations. We now have to assume that before long they will become more widespread, or even commoditised.
“But Anthropic isn’t releasing Mythos so we don’t need to worry!”
It is true that Anthropic is currently withholding the release of Mythos because of the potential implications if it was employed maliciously. But we only have to look at the neck-and-neck competition between frontier model developers around the world to recognise if one makes an advance today, others are likely to catch up tomorrow. We have to assume that other models will be as capable soon, and may not be held back from the market.
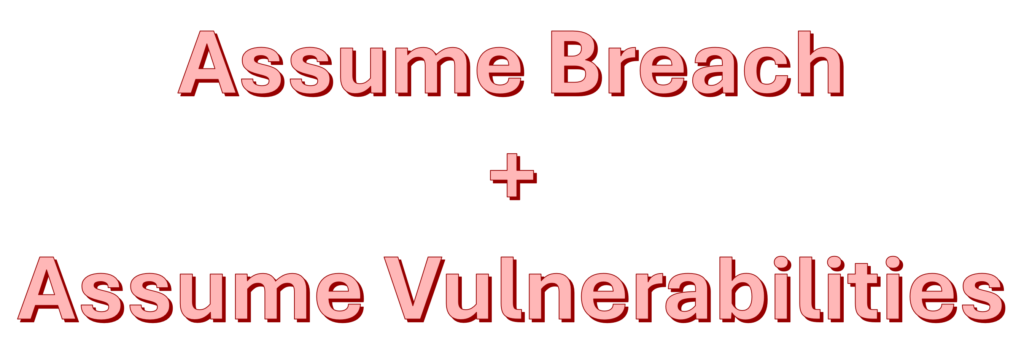
There has been a growing philosophy for some time that prevention will never be total and organisations need to operate on the assumption that a breach is inevitable. If you assume a breach is likely to happen then the need for detection, containment, damage limitation, response, and recovery all become far more important. The NCSC’s annual review for 2025 (It’s time to act – NCSC Annual Review 2025) used evidence from the significant increase in serious attacks to strongly reinforce that organizations must move beyond purely defensive strategies and adopt an “assume breach” mindset to tackle the evolving threat landscape.
In the post Mythos world we need to add “assume vulnerabilities” to that mindset. This state of affairs doesn’t just increase the likelihood of the entry level breach. Vulnerabilities need to be assumed to be everywhere. That entry level breach is just the first step, and gives the threat actor access to exploit any other vulnerabilities that exist within reach of their foothold.

Now, even a perfect vulnerability management regime is inadequate. Because we are assuming that there will be high risk vulnerabilities that not even the vendor is aware of. This new state of affairs has the potential to change the threat landscape by an order of magnitude.
“So, how do we respond to this new situation?”
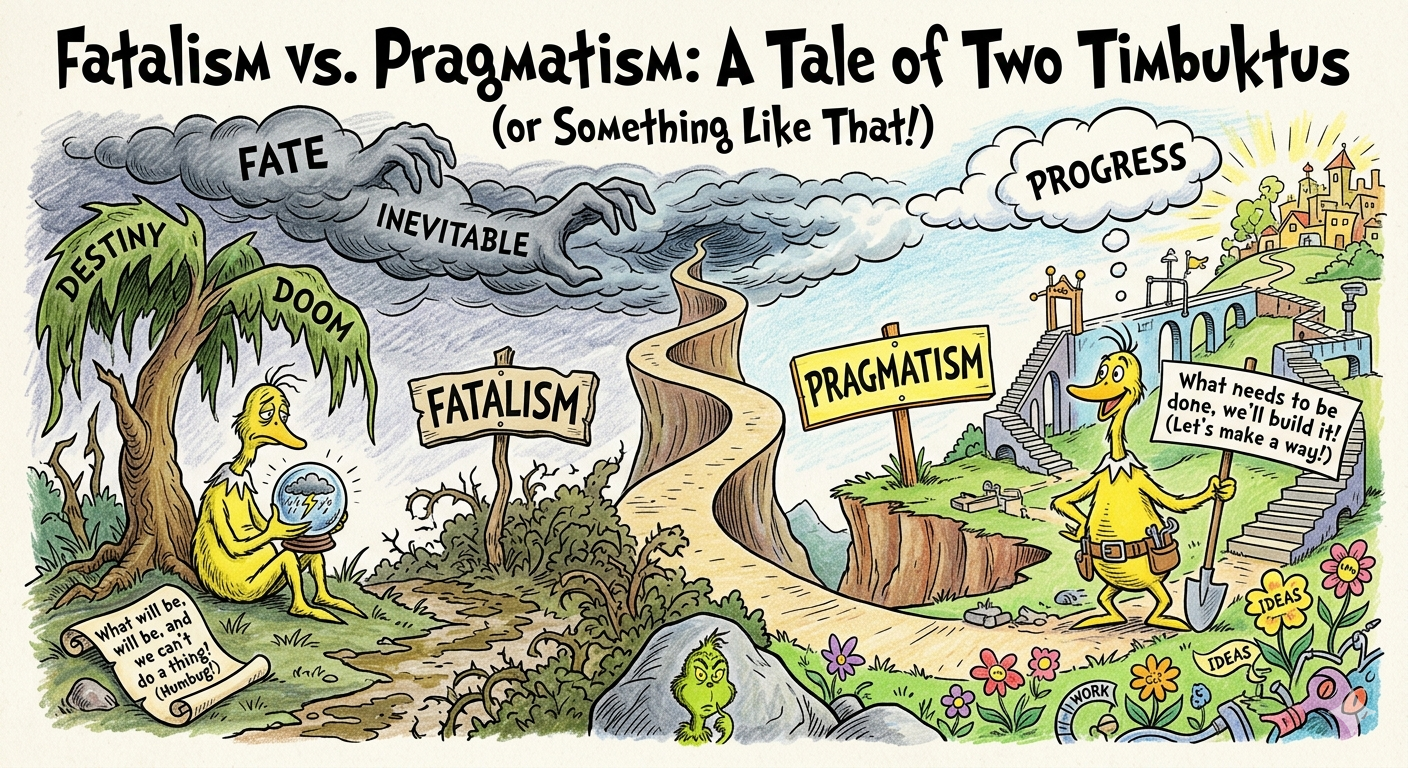
The alluring appeal of fatalism
15 years ago when the very real threat of cyber attack by nation states became recognised in the mainstream it frequently prompted a fatalistic response. I often heard phrases like “If the Russian FSB or GRU, or the Chinese MSS or PLA want to break in, they will and there isn’t much I can do to stop them!”. At a simplistic level it made sense. And at an extreme level it is undoubtedly true; if your organisation is a priority target then your ability to resist a determined attack by a well resourced and capable nation state will be limited.
But not all attacks are equal. Even nation state ones. The fact that in a narrow set of circumstances all is doomed doesn’t mean that all resistance is futile. The operational impact of the recent major cyber attack on Coop was significantly less than the similar attack on M&S at the same time. Ukraine’s critical national infrastructure and essential services were not “hacked back into the stone age” in 2022 (or since) despite having the full might of the Kremlin and its affiliated “cyber militia” thrown against it.
Fatalism is an attractive notion. If you assume all is doomed and the worst doesn’t happen then you can claim to have been lucky; if Armageddon does arise then you were right all along. None of your actions, or inaction, can be blamed.
It would be easy for us to slip back into this way of thinking. “Why bother applying patches, when the threat actors will be exploiting vulnerabilities that aren’t even known about”.
Choose life; choose pragmatism
Choose radical segmentation, ruthless identity management and practiced contingency plans
History has shown that economics work in defence. If you make the act of attacking harder, and more expensive, then eventually most threat actors will conclude that there is a better return on investment elsewhere.
“So how can we turn the economics in our favour?”
Radical Segmentation
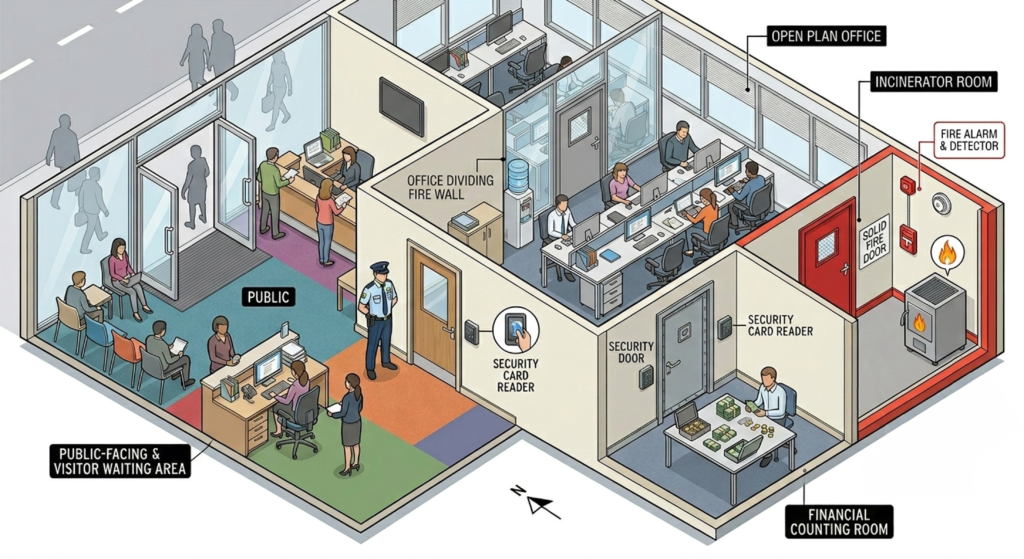
If everything in your business was flammable, and there was the very real risk that something might catch fire at any moment, what would you do? You probably wouldn’t stack everything up in a single location where one small fire would burn everything to the ground. You would introduce fire-doors, fire-proof walls, alarms and sprinklers. You would probably move the more valuable things away from the items that need to be handled every day.
If we work on the assumption that something is likely to be breached. And if we also work on the assumption that everything has vulnerabilities. Then we need to ensure that one system can only see and access another system if there is a compelling business reason for this integration. This needs to be done at a network level, rather than an interface one, because vulnerabilities present interfaces of their own that are not being managed.
Segmentation is not new, but it is harder than the convenience of a flat network. It requires the organisation to understand its portfolio of systems and how they need to interact with each other. It demands the discipline to treat every interconnection is a risk that needs to be justified with business benefit and control. It doesn’t tolerate the habits that have been built up over the last thirty years of employing a single, flat network so that we can connect everything to everything.
Ruthless Identity Management

Segmentation without gate keepers is just a more expensive flat network. Those gate keepers need to make judgements based on identity; both human identities (users) and increasingly non-human identities (devices, other systems and services). Relentlessly asking two key questions.
Who is trying to access the resource?
How have they identified themselves; have they presented multiple strong factors, or a simple username and password that could be being used across fifty other websites? On what basis do I trust that the identity is valid; are they a vetted member of staff who’s identity was validated in person before employment, or are they a general member of the public who has identified themselves as Jane but could just as easily be John?
As Peter Steiner’s now famous cartoon in the New York Times from 1993 said “On the Internet, nobody knows you’re a dog”. So we need to start on the basis that everything and everyone is a dog, until proven otherwise; and that proof needs to be revalidated constantly.
Does it have the authority to access the resource?
Identity is only the table stake. The gate keepers also need to be able to satisfy themselves that the identity is authorised to access the resource. This authority will be influenced by many factors:
- Does the identity fulfil a role that sometimes requires access to the resource?
- Is the identity currently conducting a task that requires access to the resource now?
- Does the identity’s current posture meet the required conditions; e.g. for a sensitive asset is it attempting access from a fully managed and assured device or one that might be their 13 year old son’s gaming laptop?
- Is the behaviour – the context around the request – normal or suspicious?
- Are we in a heightened state of threat that would advise blocking non-critical access requests?
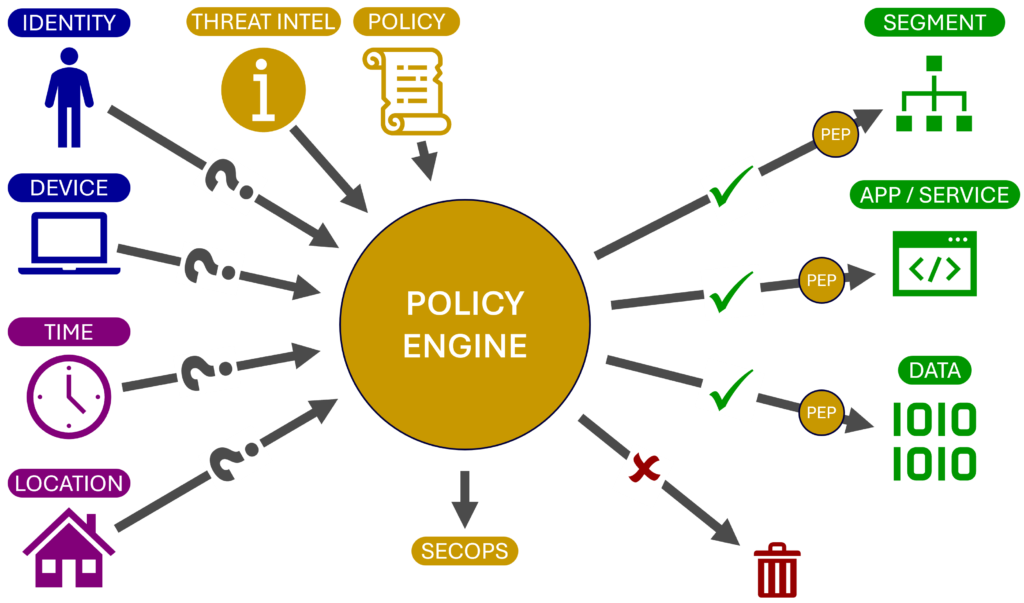
The objective is a well managed identity fabric able to make dynamic decisions on a case by case basis. No simple task, but one that can then prevent the fire spreading quickly across a business environment. It also creates an environment where fire-doors on routes that aren’t mission-critical can be slammed shut at the first sign of smoke.
Contingency Plans
The world isn’t static. What is convenient and efficient today, may be superfluous if the threat rises tomorrow, and downright risky in the midst of an incident the day after. But having dynamic controls that expose levers for us to pull in different circumstances is only part of the solution. We also need to decide which levers to pull in what situations. We can choose either to wing it as circumstances dictate at the time, or model the plausible scenarios (including the plausible but severe ones) and prepare contingency plans with pre-defined triggers and decision points. The lessons from the good, the bad and the ugly examples in history show that better actions are taken more promptly when the thinking has been done before the balloon goes up.
“Carry on keep carrying on”, but harder and faster
The good things you are already doing – they are probably just as important. If you already have a good vulnerability management regime then don’t stop it. Maintaining secure configuration control over devices is still vital. And if you aren’t whitelisting applications on devices you should probably start now; if you are you might want to reduce revisit the list and trim it a little. Because all of those apps will be run through the threat actors supercharged tools, and those devices are your front line.
A final (optimistic) thought
Through history, and not just the relatively recent history of cyber attacks, society has faced situations that seem catastrophic in outlook. But when revisited at a later date we frequently find that the change turned out to be more evolution than revolution. The global doom we feared was more limited. The world didn’t end.
Even evolution requires adaptation; particularly when the step change is significant. But it frequently offers us existing practices that we can use as a baseline to develop solutions.
This article points to some practices that aren’t new. But some need far wider adoption. And others, significant improvement.
Are you a Fatalist or a Pragmatist? Which of the following statements apply?
- 90% of our core assets and services exist on a single flat network
- Our approach to “Zero Trust” is still perimeter-based in nature, and little control is applied at the application or system level once access has been granted
- BYOD is part of our culture but we are confident that all our staff manage their devices responsibly
- If we limited what our people can do and access this would break down trust and limit our operational flexibility
- We know that our service accounts are a bit out of control, but its just too big a problem to solve today
- We are too small to be able to resist an attack, but nobody really knows who we are so its unlikely that we would be attacked
We might be in for a bit of a bumpy ride, but most of those who prepare for it will ride it out. What defences do you need to shore up first?